All Videos
79 videos from KamilSec
 11:16
11:16AI Meets Cybersecurity: Automating Vulnerability Analysis with Microsoft Copilot (Hands-on)
333 views
 16:31
16:31AI Automation for Business Professionals
118 views
 12:25
12:25Conducting Nessus Vulnerability Scan Results Analysis in 5 Minutes Using Pivot Table (Hands-on)
436 views
 5:47
5:47Governance Risk and Compliance (GRC)
498 views
 15:26
15:26Overview of the FedRAMP 800-53 Rev 5 New Test Case
822 views
 8:36
8:36Episode 9: Configuration Management Plan (CM-9 Explained) | KamilSec
787 views
 14:21
14:21Episode 8: System Component Inventory (CM-8 Explained) | KamilSec
579 views
 19:36
19:36Episode 7 Least Functionality (CM-7): KamilSec
970 views
 11:32
11:32Episode 6 Configuration Settings (CM-6)
1.0K views
 8:23
8:23Episode 5 Access Restriction For Change (CM-5)
442 views
 9:24
9:24Episode 4 Impact Analyses (CM-4)
439 views
 10:15
10:15Episode 3 Configuration Change Control (CM-3)
450 views
 13:47
13:47Episode 2 BASELINE CONFIGURATION (CM-2)
3.0K views
 14:18
14:18Episode 1 CONFIGURATION MGMT POLICY AND PROCEDURE (CM-1)
2.0K views
 25:12
25:12TIPS on Conducting NIST 800-53 Rev4 to Rev5 Control GAP Analysis
4.3K views
 9:46
9:46Episode 19_PUBLICLY ACCESSIBLE CONTENT_ (AC-22)
1.4K views
 8:00
8:00Episode 18_INFORMATION SHARING_ (AC-21)
721 views
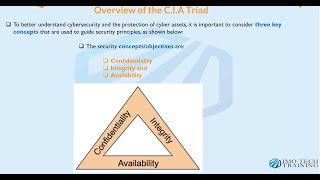 23:16
23:16Excerpt from the IMO Tech's RMF Training During Week 1
2.4K views
 10:30
10:30Episode 17_USE OF EXTERNAL SYSTEMS_ (AC-20)
811 views
 11:38
11:38Episode 16_ACCESS CONTROL FOR MOBILE DEVICES_ (AC-19)
706 views
 6:31
6:31Episode 15_WIRELESS ACCESS_ (AC-18)
1.6K views
 9:08
9:08Episode 14_REMOTE ACCESS_ (AC-17)
1.4K views
 7:48
7:48Episode 13_Permitted Actions Without Identification and Authentications_ (AC-14)
1.0K views
 7:34
7:34Episode 12_Session Termination_ (AC-12)
1.3K views
 7:40
7:40Episode 11_Device Lock Control_ (AC-11)
1.3K views
 7:07
7:07Episode 10_Concurrent Session Control_ (AC-10)
1.4K views
 8:17
8:17Episode 9_Previous Logon Notification_ (AC-9)
1.0K views
 9:39
9:39Episode 8_SYSTEM USE NOTIFICATION_ (AC-8)
1.7K views
 8:55
8:55Episode 7_UNSUCCESSFUL LOGON ATTEMPTS_ (AC-7)
2.1K views
 10:11
10:11Episode 6_LEAST PRIVILEGE_ (AC-6)
2.1K views
 11:47
11:47Episode 5_SEPARATION OF DUTIES_ (AC-5)
2.0K views
 16:01
16:01Episode 4_INFORMATION FLOW ENFORCEMENT (AC-4)
3.1K views
 7:55
7:55Episode 3_ACCESS ENFORCEMENT (AC-3)
2.9K views
 16:24
16:24Episode 2_ACCOUNT MANAGEMENT (AC-2)
4.5K views
 10:42
10:42Episode 1 ACCESS CONTROL POLICY AND PROCEDURE (AC-1)
7.9K views
 21:07
21:07Information System Contingency Planning (ISCP) Overview (SP 800-34 Rev 1)
6.3K views
 36:28
36:28IT and Computer Incident Response Process Overview (NIST SP 800-61 Rev 2)
8.8K views
 10:39
10:39Roles and Responsibilities for Key Participants in Risk Management Framework (RMF)
3.6K views
 10:18
10:18RMF and SDLC Considerations in Organizations
5.1K views
 54:43
54:43RMF POA&M Creation and Management (Hands-On Approach)
32.6K views
 30:50
30:50Conducting Nessus Vulnerability Scan Results Analysis Using Excel Spreadsheet (Hands-on)
40.5K views
 27:10
27:10TIPS FOR DEVELOPING AND REVIEWING SECURITY ASSESSMENT PLAN (SAP)
11.4K views
 19:12
19:12Some Important Tips For Reviewing and Updating System Security Plan (SSP)
10.6K views
 6:37
6:37Distinction Between Information Security and Cybersecurity
3.5K views
 16:29
16:29The Core Daily, Weekly, Monthly and Annual Responsibilities of an ISSO
11.7K views
 24:12
24:12Security Control Assessment (SCA) Process Overview
32.8K views
 36:48
36:48Hands-On Security Control Testing (AC-11) Using FedRAMP Test Case Template (Determine-if Levels)
15.9K views
 25:58
25:58Relationship Between Information System PTA, PIA and System of Records Notice (SORN) - SP 800-122.
7.9K views
 10:08
10:08IT Security Documentations/Governance and IT Security Policy Templates
4.5K views
 15:41
15:41Self Security Control Assessments (NIST SP 800-171 Rev2) Vs CMMC - The C3PAOs Requirements
6.8K views
 8:25
8:25RMF Continuous Control Monitoring Step Overview
7.9K views
 10:10
10:10RMF Authorization Step
5.4K views
 15:13
15:13FISMA Law, A&A Process and RMF Process Overview and Summary
14.1K views
 43:27
43:27RMF Control Selection Process And How To Write Security Control Implementation Statements (Hands-On)
45.3K views
 15:31
15:31Relationship Between Risk Analysis, Risk Assessment, And Risk Management (SP 800-30)
20.6K views
 10:55
10:55Relationship Between Vulnerability, Threat, Control And Risk As They Relate to Cybersecurity
11.2K views
 5:00
5:00How To Password Protect Files and Folder Before E-Mailing For Confidentiality
7.9K views
 27:59
27:59RMF Control Testing Of Identification and Authentication | Authenticator Feedback (IA-6)
6.8K views
 24:33
24:33Overview Of The Significant Changes in NIST SP 800-53 Rev 5 and Review of SP 800-53B
14.7K views
 27:28
27:28Encrypting Your E-Mails Using PGP Mailvelope For Confidentiality
16.0K views
 13:53
13:53How To Improve Your Computer Speed and Performance
527 views
 25:47
25:47Protect Yourself From Phishing Attacks: Learn Email Header and Suspecious Link (Malware) Analysis.
14.0K views
 11:47
11:47Phishing: How Easy It Is For Hackers To Spoof Your E-Mail Address.
3.2K views
 82:47
82:47RMF Security Control Testing Hands On (Using SP 800-53 and 800-53A)
33.2K views
 71:53
71:53NIST RMF System Categorization Step Hands On (Using SP 800-60 Vol II)
64.8K views
 17:04
17:04Searching The Web Like A Pro (Google Dorks)
6.9K views
 30:34
30:34Basic Wireshark Skills for Beginners
1.4K views
 35:01
35:01NMAP Skills for Ethical Hacking and Pentesting Beginners
939 views
 16:14
16:14Using Netstat Utility to locate suspecious hack on Windows Machine and how to delete the backddoor
13.1K views
 10:15
10:15Protecting Your Browsers Against Security and Privacy Vulnerabilities
448 views
 17:45
17:45How To Effectively Manage And Protect Your Passwords (KeePass)
532 views
 11:18
11:18Demonstrating Difference Between HTTP and HTTPS Protocols Using Wireshark
3.0K views
 15:36
15:36Downloading and Installing Free Nessus Vuln Scanner on Windows (Nessus Home Essential)
20.7K views
 5:57
5:57Downloading and Installing the latest and greatest Kali Linux 2020.1(Offensive Security ready image)
2.7K views
 9:41
9:41Using Macchanger to change Network Interface MAC Address
1.5K views
 6:40
6:40Downloading and Installing VirtualBox and Activating NatNetwork
431 views
 4:28
4:28Changing Network Interface MAC address manually on Kali Linux
1.1K views
 52:14
52:14FedRAMP Process Overview
22.4K views
 120:07
120:07Nessus Scan Essentials And Scan Analysis (Hands-On)
33.8K views