Is this your channel?
Day 7 Palo alto on Azure cloud. Understand VNETs connectivity| Palo alto Firewall initial Config
265 views· 8 likes· 18:06· Mar 22, 2026
Join this channel to get access to perks: https://www.youtube.com/channel/UCBujQdd5rBRg7n70vy7YmAQ/join
About This Video
Frequently Asked Questions
🎬 More from Bikash's Tech

#paloaltofirewalltraining | Day 50 | What is High Availability ? How it works ?
112 views

#paloaltofirewalltraining | Day 49 | What is Global Protect HIP and how it works ?
233 views
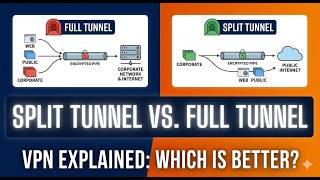
#paloaltofirewalltraining | Day 48 | What is split tunnel and what is full Tunnel ? how it works.
479 views
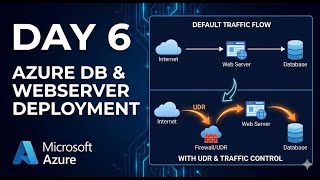
Day 6 Palo alto VM-Serise on Azure cloud. How Traffic flow works in Azure Cloud
407 views
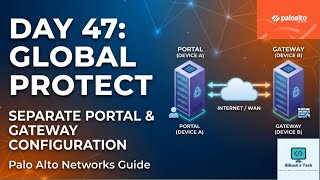
#paloaltofirewalltraining | Day 47 | How to Configure Global Protect Portal and Gateway
464 views

#paloaltofirewalltraining | Day 46 | How to Configure Global Protect VPN with AD Authentication
762 views